2 minutes
Hiding junk code using IDA scripting
what is Junk ?
A malware writer can create a malware program and then by inserting junk code into it he can create 100 unique malware with the same functionality. And when you use encryption and runtime packaging, it makes it more difficult for an anti-virus scan engine to detect matching patterns in the malware code. Some Antivirus software uses sandboxing techniques to detect malicious functions in an obfuscated programs. But we should also understand that new malware is intelligent enough to detect a sandbox environment and they can change the behavior during runtime.
when i open malware file into IDA its show’s me a tiny size of data and large size of instructions,
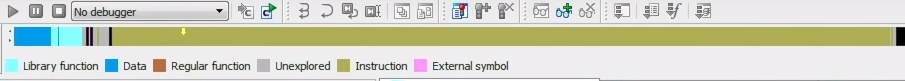 code and data sections
code and data sections
i am sure at this point that this malware in packed and having a multiple junks inside the instructions, so when i open the graph view i notice that in code there are multiple mov al instructions
in this code so properly it’s hard to hide all junk instructions manually, so we can use an IDA script to hide all unusual instruction
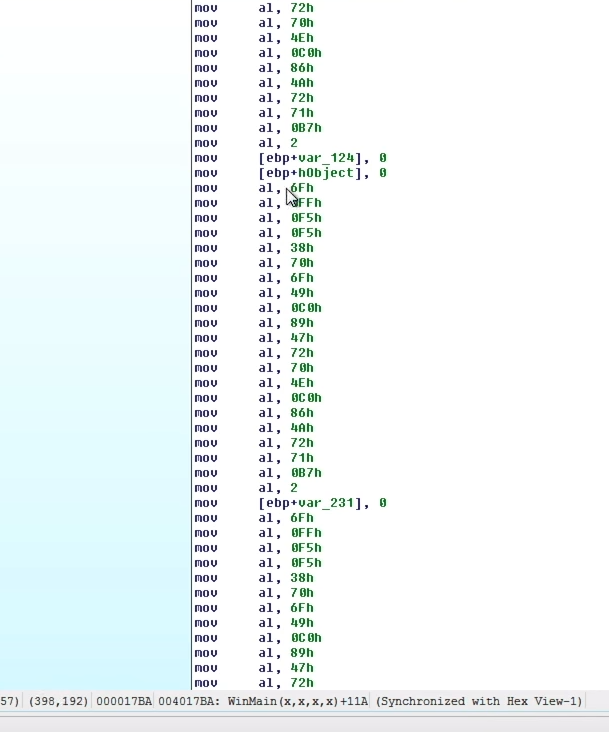
Junk codes
so far mov al instruction moves into al that’s a lower bit of the register, I never seen this type of calls in a row because you would just be replacing the byte that you moved in the last call makes no sense, safe side we are hiding only more than 4 mov al instructions in a row
the script is going through all the sections and checks whether it contains mov al instructions or if he found more than 4 mov instructions its hide that junk code.
run script:
- shortcut alt + F7 -> select script
- file -> script file… -> select script

as we can see script hide all the move al instructions.
malware sample: https://malshare.com/sample.php?action=detail&hash=f834f898969cd65da702f4b4e3d83dd0
The Beginner’s Guide to IDAPython: https://leanpub.com/IDAPython-Book